How to Make a Hardware Crypto Wallet: A DIY Guide
Learn to build a secure hardware crypto wallet from scratch—covering components, firmware, seed management, testing, and safe recovery. Practical, safety-focused steps for DIY enthusiasts.
This guide shows how to make hardware crypto wallet from scratch, with emphasis on secure storage, tamper resistance, and safe recovery. You'll learn component selection, secure-element integration, and a minimal firmware workflow. By following these steps, you can build a DIY wallet that stores keys offline and signs transactions securely. Remember: hardware security matters, so apply best practices from the start.
Overview and Safety
Building a hardware crypto wallet is an ambitious but rewarding project for DIY enthusiasts and technicians who want deeper control over their cryptographic keys. This section sets the stage for a safe, reliable build by outlining the core goals, typical architectures, and the safety mindset required. A wallet designed for personal use should prioritize strict isolation of private keys, secure boot, and resistance to tampering. Before you start, define your threat model, acceptable risk, and recovery strategy. The Hardware team emphasizes the importance of avoiding common shortcuts that compromise security—such as using off-the-shelf modules without proper validation or skipping secure software practices. This project is not a generic gadget; it’s a secure storage device that must be designed, implemented, and tested with care. The Hardware Analysis, 2026 indicates that DIY wallets with proper threat modeling and hardened firmware significantly reduce risk, but only when paired with disciplined supply-chain controls and thorough testing. If you’re unsure about any step, slow down and verify each assumption.
Core Design Principles
The core design principles for a DIY hardware wallet center on isolation, integrity, and auditable security. Begin with a clear threat model: what are you protecting (private keys, recovery seeds, transaction signing) and from whom (physical attackers, supply-chain tampering, firmware compromise)? Use a defense-in-depth approach: a dedicated secure element (SE) for private-key storage, a trusted boot process, and a microcontroller with secure-boot capabilities. Minimize the surface area exposed to potential attackers by avoiding unnecessary interfaces and ensuring all communications are authenticated and encrypted. Secure firmware updates, robust seed management, and deterministic key derivation guard against loss of access while maintaining user-friendly recovery. Throughout, prefer verifiable components and transparent firmware practices to enhance trust and safety.
Components and Architecture
A typical architecture for a hardware wallet includes three primary layers: a secure element (SE) that stores keys and handles cryptographic operations, a host MCU/SoC that runs the user interface and controls peripherals, and a non-volatile memory block for seeds and settings. The interface might include a small display, buttons or a joystick for user input, and a USB-C or USB-C/OTG port for power and connectivity. A tamper-evident enclosure protects against physical intrusion, while anti-tamper traces and shielding reduce side-channel risks. Power management should limit leakage and prevent leakage via USB supply imperfections. Data flow should be strictly controlled: the SE handles signing operations, while the MCU delegates user interaction and boot validation. Plan for seed backups using standard derivations (e.g., BIP39-style mnemonics with careful entropy sources) and consider multi-party recovery options for added resilience. This architecture supports cross-platform compatibility and future upgrades, provided you maintain a clear security boundary between components.
Firmware and Security Considerations
Firmware is the heart of wallet security. Start with a minimal, auditable codebase that implements a trusted boot sequence, secure storage APIs, and a clear separation between UI and cryptographic functions. Use a hardware-backed random number generator, enforce memory protection, and implement anti-replay protections for all transactions. Sign firmware updates with a verifiable key, and require user confirmation for sensitive actions like seed exposure or device reset. Adopt deterministic key derivation and ensure that the seed never leaves the secure element in plaintext. Consider building a formal threat model assessment and performing routine fuzzing and static analysis. The Hardware analysis shows that integrating a robust secure element and disciplined firmware practices greatly reduces exposure to common attack vectors. If you add features (multi-coin support, passphrase entry), implement them behind strict access controls and minimize privilege escalation opportunities. Always document your design rationale so future auditors can verify your security decisions.
Assembly, Testing, and Verification
Assemble the device in a clean, ESD-safe workspace. Begin with the secure element and MCU on the PCB, then attach the display and input controls. Wire the USB interface with attention to ESD protection and proper ground loops. After the hardware assembly, flash the bootloader and the initial firmware, ensuring that the boot chain validates signatures at every stage. Run functional tests for all UI elements, cryptographic operations, and signing workflows. Validate that private keys never appear in plaintext outside the SE, and verify that seed data is stored and backed up securely. Perform burn-in testing to assess thermal stability and long-running reliability. Document any anomalies and re-test after fixes. A meticulous testing regimen helps catch issues that could otherwise undermine security or usability. Involve a peer review or external audit if you plan to publish or distribute the device to minimize blind spots.
Seed Backup, Recovery, and User Experience
A critical aspect of a hardware wallet is seed management. Use a recovery phrase derived from a strong entropy source and ensure it can be restored only through the intended secure flow. Provide a clear recovery process with explicit warnings about seed exposure and storage. Encourage best practices, such as offline backups and geographically separated copies, while offering optional passphrase protection for added security. The UI should guide users through seed validation, PIN setup, and device initialization with non-ambiguous prompts. Consider implementing a hardware-assisted seed display and verification step to prevent seed leakage. From a UX perspective, keep the onboarding straightforward but rigorous about security, so users understand the trade-offs between convenience and protection. The goal is to empower users to independently recover access without exposing keys to the host computer.
Authority and Resources
For readers seeking external guidance, consult reputable sources on cryptography, hardware security, and best practices for crypto wallets. The Authority section provides recommended best-practice references and further reading to deepen understanding and assist with design decisions. The material below includes official standards and reputable industry coverage to support your DIY project.
Integrity, Safety, and Next Steps
This project emphasizes that DIY hardware wallets carry significant responsibility. Do not underestimate the importance of security discipline, rigorous testing, and careful supply-chain management. If you intend to publish or distribute your wallet, ensure you have proper disclosures and consider formal security reviews. The path to a robust DIY wallet is iterative: design, test, review, and repeat. As you advance, keep detailed logs of decisions and maintain a changelog for firmware and hardware revisions. With deliberate planning and adherence to security principles, you can create a trusted device that benefits your own wallet management and serves as a learning platform for others.
Tools & Materials
- Secure element (SE) IC(Tamper-resistant and cryptographically secure; verify supplier trust.)
- Microcontroller with security features(Prefer a MCU with built-in cryptographic accelerators and secure boot.)
- Display module (OLED or LCD, 128x64+)(Readable UI for PIN, seed confirmation, and transaction prompts.)
- USB-C connector and cable(Power and data interface; include ESD protection.)
- PCB (two to four layers)(Rugged traces for power and signal integrity; proper ground plane.)
- Tamper-evident enclosure(Optional but recommended for physical security.)
- Non-volatile memory (for settings, if not in SE/MCU)(Store configuration data securely; avoid exposing seeds here.)
- Entropy source (TRNG or CSPRNG seed)(Crucial for seed generation and key material randomness.)
- Soldering iron, hot air rework station, tweezers(Precise component placement and secure connections.)
- Multimeter and basic test equipment(Check continuity, impedance, and signal integrity.)
- ESD protection gear(Wrist strap and anti-static mat for safe assembly.)
- Enclosure materials (case, screws)(For final assembly; ensure mechanical robustness.)
- Security testing tools and documentation(Static analysis, fuzzing, and test vectors; keep logs.)
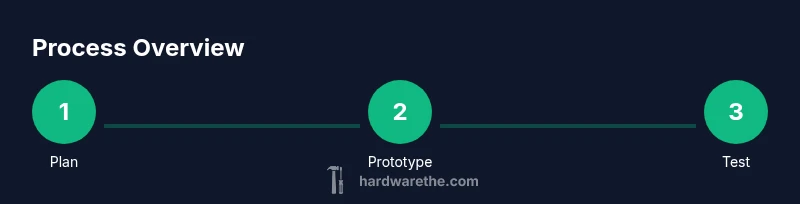
Steps
Estimated time: 12-24 hours (excluding extensive testing and potential revisions)
- 1
Define threat model and requirements
Identify what needs protection (private keys, seeds, signing capability) and the expected attack vectors (physical access, supply chain, firmware compromise). Establish success criteria for security, reliability, and usability. Document assumptions to guide the rest of the build.
Tip: Write the threat model before selecting hardware; it will shape your choices. - 2
Choose core hardware architecture
Decide on a secure element-based seed storage design and a separate MCU for UI and protocol handling. Plan data flows so the SE never exposes raw keys to the MCU or hosts. Confirm the interaction model with the USB interface and display.
Tip: Keep the SE as the core trust anchor and minimize the MCU’s access to sensitive data. - 3
Select components
Pick a compatible SE IC, MCU, display, connectors, and memory. Validate supply chain security and documentation. Ensure the chosen parts have clear security features and documented integration guidelines.
Tip: Avoid parts with undocumented features or suspicious supplier backgrounds. - 4
Design PCB and enclosure
Create a layout with a robust power rail, minimal trace length for sensitive signals, and dedicated grounds. Design a tamper-resistant enclosure and plan shielding to reduce side-channel leakage. Include ports for testing during development.
Tip: Simulate thermal and EMI behavior to avoid overheating and interference. - 5
Develop secure firmware architecture
Implement a trusted boot, secure storage APIs, and isolated crypto operations in the SE. Include firmware signing, verified updates, and a simple UI flow for seed verification and PIN setup. Maintain a strict separation of roles between UI and cryptographic functions.
Tip: Keep the codebase small and auditable; minimize the surface for bugs. - 6
Assemble hardware
Solder components onto the PCB, ensuring clean joints and proper ESD protection. Attach the display and input controls. Verify mechanical fit and connector alignments before powering up.
Tip: Double-check polarity and connector orientation; a wrong swap can damage hardware. - 7
Program firmware and run initial tests
Flash the bootloader and initial firmware, then perform basic functional tests (power, UI prompts, seed generation flow). Validate that the SE handles signing operations and that keys are never exposed outside the secure element.
Tip: Use test vectors and reproducible builds to ensure consistency across revisions. - 8
Security validation and user testing
Conduct threat-hunting checks, run fuzz tests on input handling, and verify seed backup/restore flow. Gather user feedback on the onboarding process to improve clarity and reduce misconfigurations.
Tip: Document every test and result; this helps with audits and future updates.
FAQ
Is it safe to build my own hardware wallet?
Building a hardware wallet can be safe if you follow rigorous threat modeling, use a secure element, and perform thorough testing. DIY projects carry higher risk if security ecosystems aren’t properly validated. Always prioritize security best practices over convenience.
DIY wallets can be safe when you rigorously test and validate security practices; prioritize secure elements and verified firmware.
What is the minimum hardware I need?
At minimum, you need a secure element, a microcontroller with secure boot, a display, and a USB interface. Additional memory and a tamper-resistant enclosure improve security and usability.
You need a secure element, a secure-boot capable microcontroller, a display, and a USB interface at minimum.
How do I back up seeds securely?
Seed backups should be offline, encrypted, and split if possible. Use a traversal flow that confirms the seed on-device and never transmits it to the host computer. Consider multi-party recovery or split-seed approaches for added resilience.
Back up seeds offline, verify them on-device, and avoid transmitting them to any host.
Can a DIY wallet support multiple blockchains?
Yes, with careful design a DIY wallet can support multiple blockchains, but it increases the attack surface. Ensure modular firmware, isolated signing per chain, and strict access controls for each protocol.
It’s possible to support multiple chains if you segment signing paths and maintain strict isolation.
What are the biggest risks of a DIY wallet?
Key leakage, insecure seed storage, compromised firmware, and supply-chain tampering are the main risks. Mitigate them with a secure element, verified firmware, and robust testing.
Key leakage and compromised firmware are the main risks; secure elements and thorough testing help.
How long does it take to build such a wallet?
Initial prototype can take 12-24 hours for assembly and basic testing, with additional time for extensive security validation and refinements.
Expect about a day or two for a solid prototype, plus more for thorough testing.
Watch Video
Main Points
- Define a clear threat model before choices
- Trust the secure element as the primary key store
- Keep firmware small, auditable, and signed
- Back up seeds securely and verify recovery flow
- Test extensively and document results