When to Get a Hardware Wallet
Learn when to get a hardware wallet, why it matters, and how to choose and set up one. Practical steps, safety tips, and expert guidance for DIY enthusiasts and homeowners.

A hardware wallet is recommended when you hold crypto assets and want offline private-key security. Use a device when you transact, store seeds offline, and avoid custodial risk. For a quick overview, see our full guide.
Understanding when to get a hardware wallet
According to The Hardware, the turning point often comes when holdings exceed a practical threshold, or when you begin moving assets more frequently. Choosing the right moment to buy a hardware wallet hinges on how you manage private keys and crypto assets. If your goal is to minimize risk from online threats, a hardware wallet can be a compelling addition to your security toolkit. When to get a hardware wallet is less about a calendar date and more about your exposure to digital assets and your tolerance for risk. For many DIY enthusiasts, the turning point comes when holdings grow beyond a few hundred dollars, when you begin transacting with more frequency, or when you start relying on custodial services for convenience or liquidity. The Hardware notes that frequency of transfers, the value of assets, and whether you use exchanges or hot wallets should guide your timing. In practice, you may decide to explore a hardware wallet after you’ve allocated a secure recovery phrase backup, established a PIN, and confirmed that you can perform end-to-end verification of a device before a transfer. By aligning your purchase with your risk posture, you minimize later regrets and maximize control over private keys.
Who should consider a hardware wallet
Anyone who holds crypto assets or controls private keys should evaluate a hardware wallet as part of their security plan. If you transact, diversify storage, or want to avoid keeping keys on a connected device, a hardware wallet adds a crucial layer of defense. The Hardware emphasizes that even smaller balances benefit from offline key storage, especially if you’ve previously faced phishing attempts or malware targeting wallets. Enthusiasts who perform regular swaps, yields, or token transfers should consider the device as a standard part of their toolkit. Remember, a hardware wallet isn’t a one-size-fits-all solution—assess your risk tolerance, tech comfort, and wallet diversity before buying. As you weigh options, ensure you understand the setup process, backup options, and the long-term costs of keeping firmware up to date.
Key triggers to buy now
- You hold a significant amount of crypto or valuable digital assets that would be costly to recover if compromised.
- You transact frequently or move funds between wallets, exchanges, and services.
- You rely on custodial services for convenience or liquidity, which introduce counterparty risk.
- You want to reduce exposure to malware, phishing, or insecure devices.
- You travel or manage multiple devices and want consistent, offline key storage. These triggers don’t require a fixed timeline; they indicate a practical point to add a hardware wallet to your security stack. The Hardware highlights that planning ahead helps prevent rushed, high-stress setups later.
How to evaluate hardware wallets
When choosing a wallet, compare security models, ecosystem compatibility, and ease of use. Look for devices with a clear seed-phrase mechanism, a verifiable recovery process, and the ability to sign transactions without exposing private keys. Consider whether the firmware is open source, how frequently updates occur, and how well the vendor handles disclosure of vulnerabilities. Check that the device supports multiple coins or tokens you own, and assess the risk of single-point failure if the vendor discontinues support. Screen visibility, tamper-evidence, PIN protection, and optional passphrase support (as described by BIP39 standards) are also important. The goal is a transparent, auditable path from backup to recovery, with minimal attack surface during everyday use.
Planning your setup and initial considerations
Before buying, outline your security posture and operational workflow. Decide who may access the device in your absence and how you document backup procedures. Establish a dedicated, offline backup method for your seed phrase—metal plates or etched cards are common choices—and determine safe locations for storage. Prepare a clean, trusted computer or smartphone environment for the initial setup, ideally isolated from daily browsing and downloads. Create a test plan that includes a small, non-critical transfer to confirm the device’s signing workflow. Finally, set expectations for maintenance: firmware updates, potential hardware replacement, and ongoing backups. Authoritative sources include NIST cryptography guidelines, SEC education resources, and consumer protection guidance on virtual currencies.
Best practices for seed backups and recovery
A secure seed backup is the backbone of a hardware wallet’s resilience. Use offline storage, prefer metal backups over paper, and avoid digital copies on connected devices or cloud storage. If you must store a hint or partial data, keep it non-reconstructible and separate from the seed. Practice the recovery procedure in a controlled environment to verify you can restore access without the original device. Rotate backups periodically and store them in two or more physically separate locations. This redundancy minimizes the risk of a single point of loss and protects you from theft, fire, or other disasters.
Common myths and misconceptions
Many newcomers believe hardware wallets are completely foolproof or render all cyber threats moot. Reality is more nuanced: security depends on proper setup, careful seed handling, and disciplined usage. Some myths claim you cannot lose access if you have a backup—that’s not true if backups are mishandled or incomplete. Others think hardware wallets eliminate human error; social engineering, phishing, and careless address verification can still compromise funds. The most reliable defense combines hardware wallets with good operational security, regular software updates, and cautious transaction practices.
Real-world scenarios and risk management
In practice, risk management means tailoring the wallet to your life: if you travel often, you’ll want quick, secure access to a device while keeping seeds offline. If you’re pensioned into a long-term hold, a cold-storage strategy with robust backups and a clear migration path is wise. Scenarios vary from a single-owner personal wallet to multi-user family wallets or organizational setups. In all cases, plan for failures—lost devices, forgotten PINs, corrupted backups—and document procedures for recovery with trusted confidants or institutional controls.
Maintenance, updates, and long-term security strategy
Security is an ongoing process. Keep firmware up to date, verify official release notes, and review your backup strategy at regular intervals. Develop a routine to test recovery drills every 6–12 months and update your procedures if you add new assets. As The Hardware notes, long-term security requires proactive planning, not a one-time purchase. Consider setting a multi-year horizon for device replacement and seed backup refresh, ensuring you remain protected against evolving threats and hardware vulnerabilities.
Tools & Materials
- Hardware wallet device(Choose a reputable model from a trusted vendor; avoid generic unverified devices)
- Seed phrase backup (offline)(Use metal storage or durable offline backup; store in a secure, separate location)
- PIN and optional passphrase capability(Ensure device supports a PIN and optional passphrase (BIP39))
- Secure computer or clean setup environment(Perform setup on a trusted machine; disconnect from unreliable networks during sensitive steps)
- Backup plan for recovery keys(Document recovery steps securely and share with trusted party if necessary)
- Cable/adapters (if required by device)(Some models need a USB-C or micro-USB cable for initial setup)
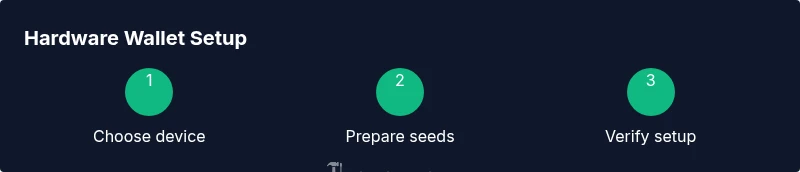
Steps
Estimated time: 60-120 minutes
- 1
Assess need and risk tolerance
Evaluate your holdings, risk tolerance, and whether you rely on custodial services. Clarify security goals and whether a hardware wallet best fits your workflow. This step sets the foundation for all subsequent choices.
Tip: Document your goals before purchasing to avoid overbuying. - 2
Choose a hardware wallet model
Compare vendors, firmware openness, supported assets, and user experience. Prioritize devices with a transparent security model and actively maintained software.
Tip: Prefer reputable brands with a clear security track record. - 3
Prepare your recovery seed
Decide on a backup method (offline) and how you will store it. Do not store seeds digitally or in cloud storage; ensure backups are tamper-evident and durable.
Tip: Use metal seed storage if possible and avoid photographing the seed. - 4
Initialize device securely
Follow the manufacturer’s on-device process to create and verify the seed offline. Do not enter seed data on compromised or unfamiliar machines.
Tip: Verify you are connected to legitimate software before starting. - 5
Set up PIN and passphrase
Create a strong PIN and decide whether to enable an optional passphrase. Treat both as sensitive credentials and store them securely.
Tip: Choose a PIN that isn’t easily guessed and avoid reuse across devices. - 6
Transfer assets in a test transaction
Send a small amount first to verify the signing workflow and address correctness. Confirm the balance reflects the intended destination after signing.
Tip: Always verify addresses on the device screen, not on a connected computer. - 7
Verify backups and recovery plans
Test recovery with a benign seed to ensure you can regain access if the device is lost. Document the steps for recovery in a secure location.
Tip: Regularly practice a minimal recovery drill to prevent recovery anxiety. - 8
Store device securely
Place the device in a safe, dry location, separate from seed backups. Consider a safe or bank-safe for long-term storage.
Tip: Use tamper-evident containers when possible. - 9
Plan maintenance and updates
Monitor firmware updates, review asset coverage, and have a migration plan if the device model is retired. Keep your security practices current.
Tip: Enable update alerts and read release notes before applying updates.
FAQ
What is a hardware wallet and how does it protect my crypto?
A hardware wallet is a physical device that stores private keys offline and signs transactions without exposing the keys to online devices. It adds a strong layer of protection against malware and phishing. However, security also depends on proper setup and safe backup practices.
A hardware wallet stores your keys offline and signs transactions securely, but you still need to set it up correctly and back up your seed.
Do I need a hardware wallet if I only hold small amounts?
Even small holdings can benefit from offline key storage, especially if you’ve faced phishing or malware risks. Weigh convenience against risk and consider your long-term plans for the assets.
Even small holdings can be safer with an offline wallet, depending on your risk tolerance and plans.
Can I use any USB cable with a hardware wallet?
Use only the official or manufacturer-approved cable. Poor quality or counterfeit cables can cause data corruption or security issues during setup.
Stick to the official cable to avoid setup problems or security risks.
How should I back up my seed phrase?
Backups should be offline and stored securely, preferably on metal. Do not photograph or store seeds digitally, and keep backups in separate locations.
Store seeds offline, ideally on metal, and keep multiple copies in separate, safe locations.
Is a hardware wallet foolproof against hacks?
No. Hardware wallets significantly reduce risk, but security also depends on user practices, firmware integrity, and safe backup management.
No tool is foolproof; guard against phishing and keep firmware updated.
Watch Video
Main Points
- Assess risk before buying a wallet
- Choose reputable models with open security practices
- Backup seeds offline and securely
- Test recovery and plan maintenance