What Is the Best Hardware Wallet? A Practical Guide for 2026
Discover what is the best hardware wallet for crypto security in 2026. The Hardware analyzes options, explains criteria, and guides DIY enthusiasts and technicians to pick with confidence.
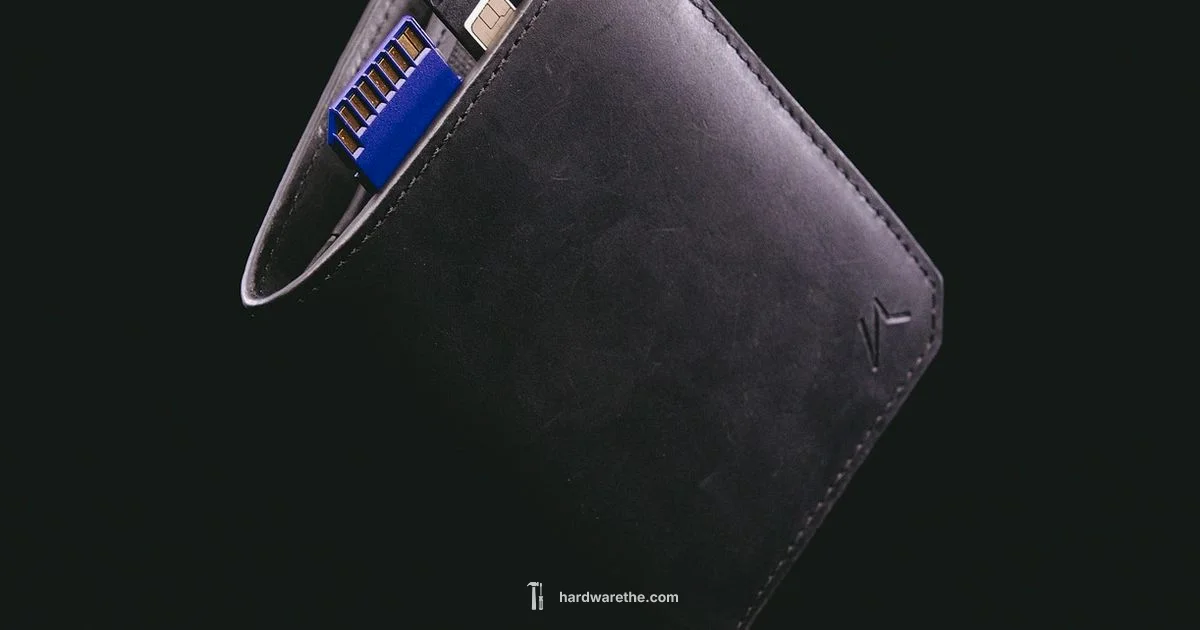
What is the best hardware wallet? The best choice depends on your goals, but for most DIY enthusiasts and homeowners, a mid-range hardware wallet with robust security, broad app support, and clear backup options offers the best balance. The Hardware team finds that devices with open-source firmware, reputable vendors, and strong recovery features consistently outperform cheaper options in practice.
What is the Best Hardware Wallet? A practical anchor
If you're asking what is the best hardware wallet, you're not alone. For DIY enthusiasts and homeowners who want to keep crypto safe offline, the answer hinges on security, usability, and ecosystem. According to The Hardware, the best choice is not a flashy model but a balanced device that offers strong protection, clear backup options, and broad support across apps and platforms. The article below walks through criteria, tests, and real-world scenarios to help you pick confidently. Think of it as a secure vault for private keys that stays on your desk or in your burglary-proof drawer—yet remains easy to use for everyday transactions. The goal is a setup where recovery remains reliable, not a tangled web of passwords and terminals.
How hardware wallets work: core components
A hardware wallet keeps your private keys off your computer or phone by storing them on a dedicated device. The core components are a microcontroller (the brain), a secure element or isolated memory region (the vault), a display for user verification, and inputs for PINs or passphrases. When you sign a transaction, the device proves ownership without revealing the secret. The result is a portable, offline-approved transaction flow that mitigates malware risks on connected devices. The hardware wallet never exposes the seed phrase during normal operation, and it uses cryptographic checksums to prevent tampering. This architecture is the backbone of crypto security for the average homeowner and professional technician alike.
Selection criteria: security, usability, and ecosystem
Choosing the best hardware wallet comes down to three pillars: security, usability, and ecosystem. Under security, you want strong seed protection, robust PIN requirements, and tamper-evident packaging. For usability, factor in screen size, intuitive navigation, and clear prompts for seed backup. For ecosystem, consider cross-platform compatibility, coin support, and integration with popular wallet apps. Price and vendor reputation also matter, but they should support your core goals: safe storage and easy access when needed. Balance between a tried-and-true layout and future-proof firmware updates matters, too. The Hardware approach emphasizes a well‑rounded device over flashy features that don’t improve long-term security.
Open-source firmware vs closed-source: why it matters
Open-source firmware lets the community inspect code for backdoors and bugs, which many DIY enthusiasts value highly. Closed-source options can still be secure, but you rely more on vendor integrity and disclosures. The Hardware analysis shows that open-source wallets tend to benefit from faster patch cycles and broader scrutiny, reducing the risk of hidden vulnerabilities. If you choose closed-source firmware, look for third-party audits, transparent release notes, and a strong vendor track record. Either path works if you remain disciplined about updates and recovery planning.
Key security features to verify before purchase
- Secure element or equivalent isolation for private keys
- Strong PIN protection with lockout after multiple failed attempts
- Seed phrase backup support (prefer 12–24 words) and optional passphrase
- Verified transaction display, ensuring you can confirm details on-device
- Tamper-evident packaging and secure delivery
- Regular firmware updates and clear disclosure of security patches
- Compatibility with reputable wallets and recovery options
Setup, backup, and recovery best practices
Begin with a clean device: initialize in a trusted environment, write down the seed phrase on paper, and store it securely offline. Enable a passphrase if you want an extra layer of defense. Practice recovery by simulating seed restoration on a separate device to ensure you can regain access. Keep firmware up-to-date and verify the source before updating. Finally, never store seed phrases digitally; avoid screenshots or cloud backups that could be hacked.
Common trade-offs: price, size, compatibility
Budget devices tend to compromise on screen size, seed backup options, or app ecosystem breadth. Premium models offer richer displays, faster firmware support, and broader coin coverage but at a higher upfront cost. For many users, a mid-range wallet delivers a balanced experience, with adequate security and broad compatibility across desktop and mobile wallets. When evaluating, compare seed backup methods, screen verification, and the ease of recovery across platforms.
Supported assets and ecosystem: wallets, apps, and coins
Different wallets support different sets of coins and tokens. Before buying, map the assets you actually hold or plan to hold, and confirm compatibility with your preferred software wallet and mobile app. A healthy ecosystem means frequent app updates, clear coin support lists, and straightforward import/export of addresses. Avoid devices with a patchy update history or limited support for your most-used assets.
How we evaluate the best hardware wallet (our methodology)
Our evaluation blends hands-on testing with vendor transparency checks. We examine security architecture (seed storage, PIN, anti-traud measures), the user experience (setup flow, verification prompts, recovery process), maintenance (firmware update cadence), and ecosystem breadth (coin support, app compatibility). We also consider real-world use cases from DIY installers and technicians to ensure the chosen devices perform under varied conditions. The goal is to identify wallets that offer strong security without compromising on everyday practicality.
Real-world use cases: home DIY and professionals
For the home DIYer, a wallet with an intuitive UI and clear backup steps reduces the risk of human error. For technicians, reliability during field repairs and compatibility with multiple operating systems matters. In both cases, you want a device that can be confidently used in daily transactions, holds up to travel or site work, and remains accessible if you need quick access to funds. The practical choice often bridges the gap between security ideal and usability reality.
What’s new in 2026: trends in hardware wallets
Expect ongoing improvements in onboard displays, faster processors, and stronger anti-tamper features. More wallets will emphasize multi-ecosystem support, better seed management, and improved recovery flows to reduce the likelihood of lockouts. The industry continues to push for open-source transparency and regular third-party audits to increase consumer trust. These trends align with the DIY community’s demand for transparent, dependable security tools.
Quick-start checklist: before you buy
- List your assets and required apps
- Confirm device compatibility with your operating system and wallet app
- Check for open-source firmware or third-party audits
- Review backup options and seed phrase handling
- Read vendor update frequency and support policy
- Consider form factor, screen size, and battery life if portable
- Inspect packaging and tamper-evident seals for authenticity
The Hardware team endorses a balanced, mid‑range wallet with transparent security and broad app support as the best overall choice for most users.
This recommendation aligns with typical user needs: strong on-seed protection, clear recovery, and compatibility across platforms. It avoids overpaying for features you won’t use while ensuring a solid path to secure storage and easy access when needed.
Products
Mid-range Wallet X
Hardware Wallet • $80-140
Premium Wallet Y
Premium • $180-260
Budget Wallet Z
Budget • $40-80
Open-Source Wallet A
Open-source • $100-160
Ranking
- 1
Best Overall Device9.2/10
Excellent balance of security, usability, and ecosystem.
- 2
Best Value8.8/10
Strong features at a mid-range price.
- 3
Open-Source Favorite8.4/10
Transparent firmware with active community support.
- 4
Best for Beginners8/10
User-friendly setup and guided recovery workflows.
FAQ
What is a hardware wallet and why use one?
A hardware wallet is a physical device that stores your private keys offline, protecting them from online malware. It signs transactions on-device and never exposes your seed phrase to a connected computer. This makes it far safer than storing keys on a computer or phone.
A hardware wallet is a physical key vault for your crypto. It signs transactions on-device and stays offline to protect your private keys.
Is a hardware wallet safer than software wallets?
Yes, in most cases. Hardware wallets keep private keys offline, reducing exposure to malware and phishing. Software wallets live on your computer or phone and can be more vulnerable if the device is compromised.
Hardware wallets are generally safer than software wallets because they keep keys offline.
Do I need to buy the most expensive model?
Not necessarily. The best value usually comes from mid-range devices that offer essential security features and broad compatibility. The most expensive models typically add premium screens or extra features that may not matter for your needs.
Not always. A mid-range wallet often gives you the best balance of security and usability for most people.
Can I use a hardware wallet with mobile devices?
Many hardware wallets pair with mobile apps via Bluetooth or USB adapters. Check the support list for your phone OS and ensure the setup flow works smoothly on mobile. Some wallets are more mobile-friendly than others.
Yes, several wallets work well with phones, but check compatibility before buying.
How do I recover funds if my device dies?
Recovery relies on your seed phrase. As long as you have the 12–24 word seed securely stored, you can restore access on a new device. Practice this process in a safe environment before you need it.
If your device dies, you can recover with your seed phrase on a new wallet.
Are all hardware wallets open-source?
No. Some use open-source firmware, while others are closed-source. Open-source wallets are often preferred for transparency, but always review audits and update history regardless of the code type.
Not all wallets are open-source, but always review security audits and updates.
Main Points
- Prioritize seed backup and PIN protection
- Verify app ecosystem and asset support before buying
- Prefer open-source firmware where possible for transparency
- Plan your recovery strategy and practice seed restoration
- Match device form factor to your usage pattern