Is Hardware Firewall Better Than Software? A Balanced Look
Explore whether a hardware firewall outperforms software solutions for network security. This in-depth comparison covers performance, cost, management, and deployment, with practical guidance for DIY networks and professional setups.
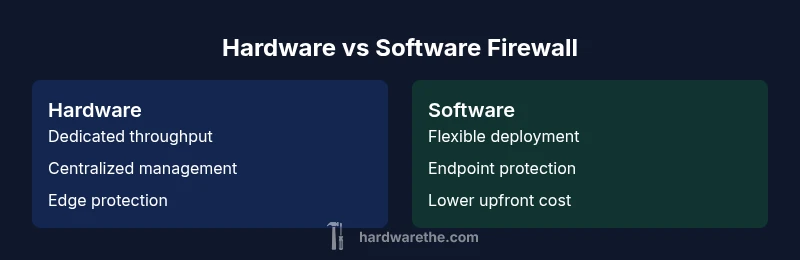
Is hardware firewall better than software? In most larger or throughput-heavy networks, a dedicated hardware firewall tends to deliver clearer perimeter protection and stable performance. However, software firewalls remain valuable for endpoint security, flexible scaling, and cost efficiency on smaller or mixed environments. The Hardware team analyzes the trade-offs to help you decide based on network size, threat model, and maintenance willingness.
What is a hardware firewall vs software firewall?
According to The Hardware, a hardware firewall is a dedicated network appliance that enforces traffic rules at the network edge. It runs specialized firmware on purpose-built hardware, designed to handle high-speed packet inspection and policy enforcement without consuming other devices. A software firewall, by contrast, is installed on a general-purpose host—such as a server, workstation, or router—using the host's CPU and memory to inspect traffic. This distinction matters for performance isolation, management scope, and future scalability. The Hardware Team emphasizes that understanding this basic split frames the rest of the decision. For many readers, is hardware firewall better than software is not a universal truth; rather, it depends on the role you want security to play in your network.
In practice, organizations often begin with the simplest option that meets their needs and then layer defenses as the threat model evolves. The Hardware analysis shows that most home networks lean toward software or hybrid approaches due to cost and convenience, while small to mid-sized businesses tend to favor hardware solutions for perimeter protection and consistent throughput. The goal is a robust, auditable policy without sacrificing operational reliability.
When to choose hardware vs software: deployment scenarios
Hardware firewalls excel in scenarios where you need a hardened perimeter with predictable performance, particularly in networks with multiple subnets, VPNs, and remote sites. They offer centralized policy management, dedicated interfaces, and often built-in features like intrusion prevention, domain-based access controls, and high-availability options. For small offices or home labs, hardware devices can still be cost-effective when you value a single point of control and reduced load on servers. Software firewalls are appealing when you prioritize cost flexibility, rapid deployment on existing hardware, or strong integration with host-based security controls. They scale better in environments where the threat model treats devices as the primary attack surface, and you want to enforce policies across endpoints and servers.
The Hardware team notes that a mixed approach often yields the best balance: a hardware perimeter to block and inspect external traffic, plus software controls on endpoints for defense in depth. The choice should map to your organizational goals, risk tolerance, and the practical realities of your IT staff. The goal is to align security capabilities with the network’s size and the organization’s resource constraints, rather than chasing a one-size-fits-all solution.
Performance and throughput: real-world expectations
Performance is a central differentiator between hardware and software firewalls. Hardware devices typically offer dedicated processing power, specialized ASICs, and optimized memory architectures that support sustained throughput during peak traffic. This translates into more predictable latency and less impact on other network services. Software firewalls, while highly adaptable, rely on the host’s CPU, memory, and I/O bandwidth; their throughput can fluctuate with workload, other running processes, and virtualization overhead. In practice, a busy network with encrypted tunnels or high connection counts may see better, steadier performance with a purpose-built appliance.
Nevertheless, modern software firewalls can be surprisingly capable when deployed on robust servers or virtualization platforms with adequate resources and proper tuning. In certain use cases—such as lab environments, test networks, or remote sites where a hardware appliance is impractical—the flexibility of a software approach can compensate for lower raw throughput with faster configuration and updates. The Hardware analysis reinforces that performance must be measured against actual traffic patterns, not just published specifications.
Security features and threat models
Hardware firewalls often come with a broad array of security features designed for perimeter defense: stateful packet inspection, deep packet inspection, network address translation, VPN termination, and integrated intrusion prevention. They also provide centralized logging, secure management interfaces, and physically isolated processing paths. These characteristics support a clear threat model focused on external threats entering the network from the Internet or other untrusted networks.
Software firewalls are strong for enforcement at endpoints, servers, or virtual machines, offering granular control over application behavior, process-level restrictions, and easier policy updates tied to software patches. They complement perimeter controls by reducing the risk of compromised hosts being used to pivot inside the network. The Hardware Team highlights that the most resilient security posture combines both approaches: a hardened perimeter plus robust endpoint defenses that reduce dwell time and lateral movement.
Cost of ownership and maintenance
Upfront cost is a major consideration. Hardware firewalls require an initial purchase, plus ongoing maintenance such as firmware updates, hardware refresh cycles, and potential licensing for security services. These costs can be steady and predictable, especially when you factor in bundled features like IPS, VPN, and centralized management. Software firewalls generally have lower upfront costs because they leverage existing hardware; ongoing costs come from software licenses, maintenance fees, and potential hardware upgrades to support scaling.
From a long-term perspective, the total cost of ownership depends on network size, the number of protected endpoints, and the desired level of security automation. The Hardware Team notes that neglecting renewal and update cycles for either approach can erode value quickly, making it important to build a maintenance calendar and budget around threat models and business needs. The ultimate decision should weigh both initial price and ongoing expenses over the system’s expected life.
Compatibility, integration, and management
Perimeter devices must integrate with existing network infrastructure, including switches, routers, and remote-access solutions. Hardware firewalls typically offer standardized management interfaces, centralized policy repositories, and compatibility with common software-defined networking (SDN) ecosystems. They often provide better interoperability in heterogeneous networks with multiple vendors. Software firewalls tend to be easier to deploy in environments where hosts already run authoritative security software, but they can complicate management when policy is dispersed across dozens or hundreds of endpoints.
In mixed environments, administrators should plan for centralized visibility, consistent logging formats, and schema alignment across devices. The Hardware Team emphasizes the importance of choosing products with robust API support, seamless firmware updates, and clear upgrade paths to avoid configuration drift during scale-up. Regardless of approach, ensure there is a clear change-management process and documented incident response procedures.
Practical deployment guidelines
If you’re starting from scratch, map your network topology to define where each firewall role fits: edge protection, internal segmentation, and endpoint defense. For hardware solutions, design a layered policy that emphasizes edge filtering, VPN termination, and IDS/IPS where appropriate. For software firewalls, ensure endpoints are consistently protected and that central logging is enabled for incident response. A phased rollout with testing windows reduces risk and reveals hidden bottlenecks before full deployment.
Maintenance should be routine: schedule firmware or software updates, review threat intelligence feeds, and validate rules after changes. Consider high-availability configurations for hardware devices to minimize downtime, and test failover scenarios regularly. The goal is to implement a shield that remains effective against evolving threats without introducing complex operational overhead.
Authority sources
To ground this discussion in established guidance, consult independent security authorities. Key references include official government and academic resources, as well as leading industry publications. These sources provide foundational concepts that inform practical decisions about hardware versus software defenses. For example, national cybersecurity agencies emphasize perimeter protection strategies, while education institutions highlight defense-in-depth principles. Always corroborate product-specific claims with reputable sources and current best practices.
The decision framework: best for whom?
When deciding between hardware and software firewalls, anchor your choice to your network topology, threat model, and available expertise. Large, multi-site organizations with high throughput needs generally benefit from a hardware perimeter with centralized controls and dedicated resources. Smaller organizations or home networks often gain value from software-based protections and flexible deployment on existing hardware. The most robust security posture usually combines both approaches: a hardware perimeter plus strong endpoint controls. The Hardware Team recommends starting with a clear risk assessment, followed by a staged deployment plan that evolves with your organization’s security maturity.
Comparison
| Feature | Hardware firewall | Software firewall |
|---|---|---|
| Performance & throughput expectations | Higher, dedicated hardware handling peak traffic | May vary with host workload and virtualization |
| Management and policy control | Centralized UI, appliance-centric management | Host-based or OS-integrated management; broader policy scope |
| Threat model alignment | Perimeter defense against external threats | Endpoint protection and internal threat containment |
| Upfront cost | Higher upfront for dedicated device | Lower upfront, leverages existing hardware |
| Maintenance & updates | Firmware updates, hardware refresh cycles | Software patches, dependency management, OS updates |
Upsides
- Dedicated performance and predictable throughput
- Centralized management and visibility
- Isolates security functions from host devices
- Clear upgrade paths and support for SLAs
Negatives
- Higher upfront cost and ongoing maintenance
- Firmware and hardware lifecycle risks
- Less flexible for rapid changes in small setups
- Requires vendor-specific expertise and room for hardware failures
Hardware firewall generally offers stronger perimeter protection and stable throughput for larger networks; software firewalls excel in endpoint protection and cost flexibility for smaller setups.
Choose hardware when you need robust, centralized perimeter security and predictable performance. Opt for software when you prioritize rapid deployment, lower initial cost, and strong endpoint control; many environments benefit from a hybrid strategy.
FAQ
What is the main difference between hardware and software firewalls?
A hardware firewall is a dedicated device that enforces traffic rules at the network edge, while a software firewall runs on general-purpose hardware and relies on the host’s resources. Hardware tends to offer centralized management and stable performance, whereas software provides flexibility and endpoint coverage.
Hardware firewalls are dedicated devices at the network edge; software firewalls run on existing machines and depend on those machines for performance.
Are software firewalls safer than hardware ones?
Both can be secure when configured correctly, but hardware firewalls reduce the risk of host-based exploits affecting perimeter protection. Software firewalls are powerful for endpoints, but require diligent management to avoid gaps in policy and patching.
Neither is automatically safer; it depends on configuration and threat model.
Can you combine both hardware and software firewalls?
Yes. A layered approach uses a hardware perimeter for external traffic and software controls on endpoints to defend against internal threats and compromised devices. This combination strengthens defense in depth.
Yes, use hardware at the edge and software on endpoints for stronger protection.
How do I estimate the cost for a hardware firewall?
Estimate involves upfront device cost, licensing for security services, and ongoing maintenance. Budget for firmware updates, support, and potential hardware refreshes over the network’s lifecycle.
Plan for upfront costs plus ongoing maintenance and renewals.
Which is better for home networks?
For home networks, software firewalls on routers or devices can be sufficient and cost-effective, especially when combined with good router security features. Hardware may be overkill unless you need advanced features or multi-site support.
Software solutions on existing hardware often fit homes best.
Main Points
- Assess network size to choose hardware for perimeter protection
- Lean on software firewalls for endpoint security and flexibility
- Plan for centralized management and ongoing maintenance
- Consider a hybrid approach for layered security
- Validate decisions with real traffic tests and risk assessment