Hardware Firewalls: A Practical Guide for 2026
Discover how hardware firewalls differ from software, essential features to look for, and practical steps to select, deploy, and maintain a secure home or small office network in 2026.
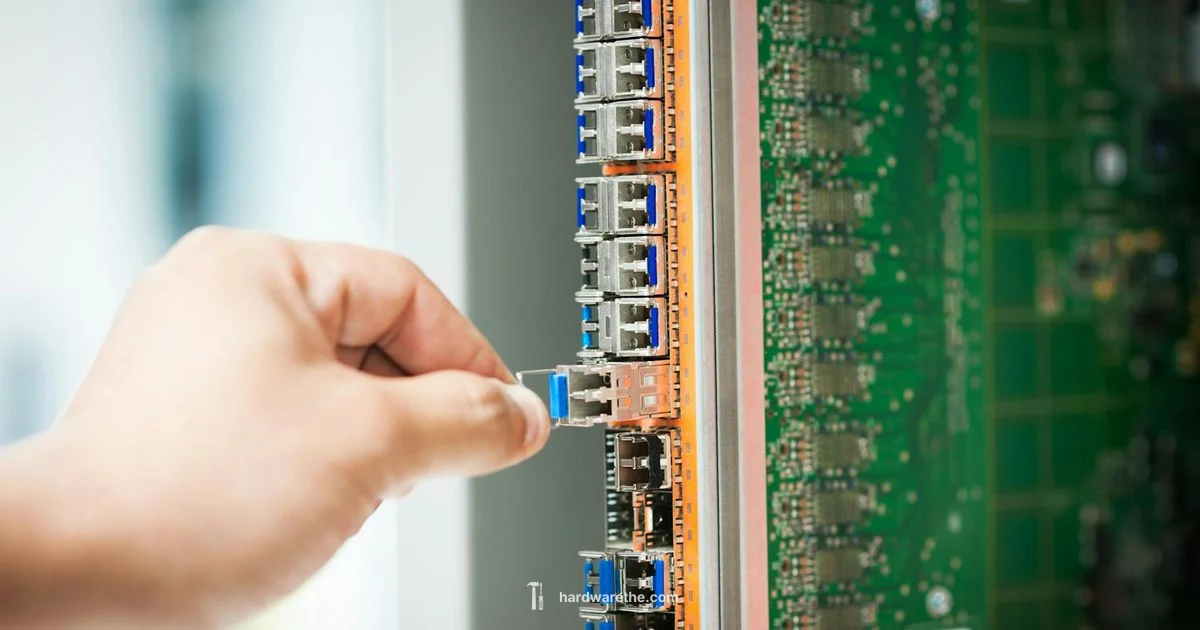
Hardware firewall is a dedicated networking device that monitors and filters traffic between networks based on predefined security rules, providing perimeter protection independent of endpoints.
What is a hardware firewall and how it differs from software firewalls
A hardware firewall is a physical device placed at the network edge to inspect and filter traffic before it reaches your computers. In contrast, a software firewall runs on individual devices. The exact query text 'is a hardware firewalls' appears frequently in search as people seek to understand this difference. At a high level, hardware firewalls provide centralized policy management, deeper integration with network features, and predictable performance because they run on dedicated hardware. They can block unauthorized access, segment traffic, and log events across all connected devices, reducing the burden on individual endpoints. Because they operate independently of user devices, they can enforce security consistently even when endpoints are misconfigured, out of date, or offline.
Core features you should expect
Modern hardware firewalls come with a core set of features that define their value. Stateful inspection tracks active connections; deep packet inspection can examine payloads for threats; NAT translates addresses for privacy; VPN support allows secure remote access; Intrusion prevention systems (IPS) detect and block known attack patterns; Logging and reporting provide visibility into events; Easy firmware updates keep defenses current; Many models offer high availability and redundant power options for critical networks. While features vary by vendor, a good baseline includes a robust management interface, clear rule syntax, and the ability to export/import configurations. Always verify support for VPN protocols you need and whether the device can handle your expected traffic load.
Typical deployment scenarios for home and small offices
In many homes, a hardware firewall sits between the gateway modem and the internal network, creating a controlled perimeter for all wired and wireless devices. For small offices, it often serves as the central security hub with site to site VPNs, remote access VPNs for employees, and centralized quarantining of suspicious traffic. Industrial environments may require rugged, industrial grade models with extended temperature ranges and specialized interfaces. In all cases, hardware firewalls provide consistent enforcement of rules, regardless of user device security posture. They complement, not replace, secure endpoints and proper network segmentation.
How to choose a hardware firewall: a buyer's checklist
Start by defining your needs: the number of users, devices, and the required VPN capacity. Check throughput ratings for WAN and LAN interfaces to ensure the device can handle peak traffic without bottlenecks. Confirm supported security services such as IPS, malware protection, URL filtering, and application control. Consider management complexity and whether centralized management is important for your network. Look for models with a reasonable upgrade path, warranty, and ongoing software support. Finally, compare total cost of ownership across models, including licensing and potential add-ons for features you might need in the future.
Setup tips and best practices for reliable protection
Before turning anything on, make a plan for a secure default posture: block by default and only allow necessary traffic. Place the device at the network edge, ideally between the modem and the router, and use a separate management network for administrative access. Change default passwords, enable automatic firmware updates, and back up configurations regularly. Create clear rules for inbound and outbound traffic, then test with representative traffic. Enable VPNs with strong authentication and separate access controls for sensitive resources. Finally, document changes and monitor logs to catch misconfigurations early.
Common myths and misconceptions
One myth is that a hardware firewall alone will solve all security problems. In reality, it is part of a layered defense strategy that includes secure endpoints, updated software, and good network hygiene. Another misconception is that more features always equal better protection. Some features add complexity and latency; choose based on your actual risk profile. Some users assume hardware firewalls are only for large enterprises; in fact, modern units are affordable for many homes and small offices, though price rises with performance and feature depth. Finally, users sometimes expect plug and play security; while setup can be straightforward, it requires planning and ongoing maintenance to remain effective.
FAQ
What is the difference between a hardware firewall and a software firewall?
A hardware firewall is a dedicated device at the network edge that enforces security policies for all connected devices. A software firewall runs on individual devices and protects only that host. Both can be complementary, but hardware devices centralize control and typically offer higher throughput.
A hardware firewall is a dedicated device at the network edge, while a software firewall runs on a single computer. They complement each other; hardware focuses on the whole network, software on individual machines.
Do I need a hardware firewall at home or for small offices?
If you want centralized control, better traffic visibility, and stronger protection for multiple devices, a hardware firewall is worth considering. For very small networks with basic needs, a strong software firewall and router security may suffice, but hardware devices offer more robust features and easier management.
A hardware firewall is often worth it for multiple devices and centralized control, though small setups may get by with software protections and solid router security.
What features matter most when selecting a hardware firewall?
Key features include throughput enough for your network, VPN support, intrusion prevention, application control, URL filtering, centralized management, and reliable firmware updates. Some environments require high availability and redundant power. Evaluate your needs against these features.
Look for throughput, VPN support, IPS, and a solid management interface that fits your network needs.
Can a hardware firewall protect devices from malware and phishing attacks?
Many hardware firewalls include IPS and gateway antivirus or URL filtering that blocks known threats and malicious sites. However, protection is strongest when combined with endpoint protection and safe browsing practices.
Yes, many hardware firewalls can block known threats and bad sites, but they work best with good endpoint protection.
How should I place and configure a hardware firewall in a home network?
Place the device at the network edge, between your modem and router if you use one. Start with a default deny posture and gradually add rules, test connectivity, and monitor logs. Keep firmware updated and back up settings.
Put it at the edge between the internet and your internal network, start with strict rules, and keep it updated.
What are common myths about hardware firewalls?
Common myths include that hardware firewalls are only for enterprises, that more features always mean better protection, and that setup is impossible for beginners. Reality: there are affordable options for homes and small offices, and proper configuration is essential.
Common myths are that hardware firewalls are only for big companies and that more features equal better protection; in reality, proper setup matters for security.
Main Points
- Define your needs before selecting a device
- Prioritize throughput, VPN, and IPS capabilities
- Plan a secure default policy and network segmentation
- Keep firmware up to date and monitor logs regularly
- Remember hardware firewalls are part of a layered defense