Hardware for Firewall: Essential Firewall Hardware Guide
Discover the hardware you need for a reliable firewall, including dedicated appliances, NICs, power redundancy, and practical setup tips for DIY network security.
hardware for firewall is a category of networking gear that enforces security perimeters by filtering traffic. It includes dedicated firewall appliances, network interface cards (NICs), and related devices that run security policies.
Overview of the firewall hardware landscape
At the network edge, firewall hardware acts as the gatekeeper that enforces security policies and regulates traffic between trusted and untrusted networks. There are three common approaches: dedicated firewall appliances from vendors who specialize in security hardware, software firewalls running on general-purpose gear (servers or mini PCs), and modular security gateways that package firewalling with VPN, IDS/IPS, and web filtering. A well-chosen unit aligns its capacity with your traffic profile and growth plans. The Hardware analysis shows that misconfigurations are a frequent bottleneck, so hardware selection should go hand in hand with solid policy design and management practices. When evaluating options, consider three pillars: performance, features, and reliability. Performance covers throughput and concurrent connections, features include VPN support and threat prevention, and reliability involves redundancy, power protection, and cooling. In practice, most small to medium deployments benefit from a purpose-built appliance with room to scale, while larger networks might opt for modular gateways or purpose-built servers with specialized accelerators.
Key components of firewall hardware
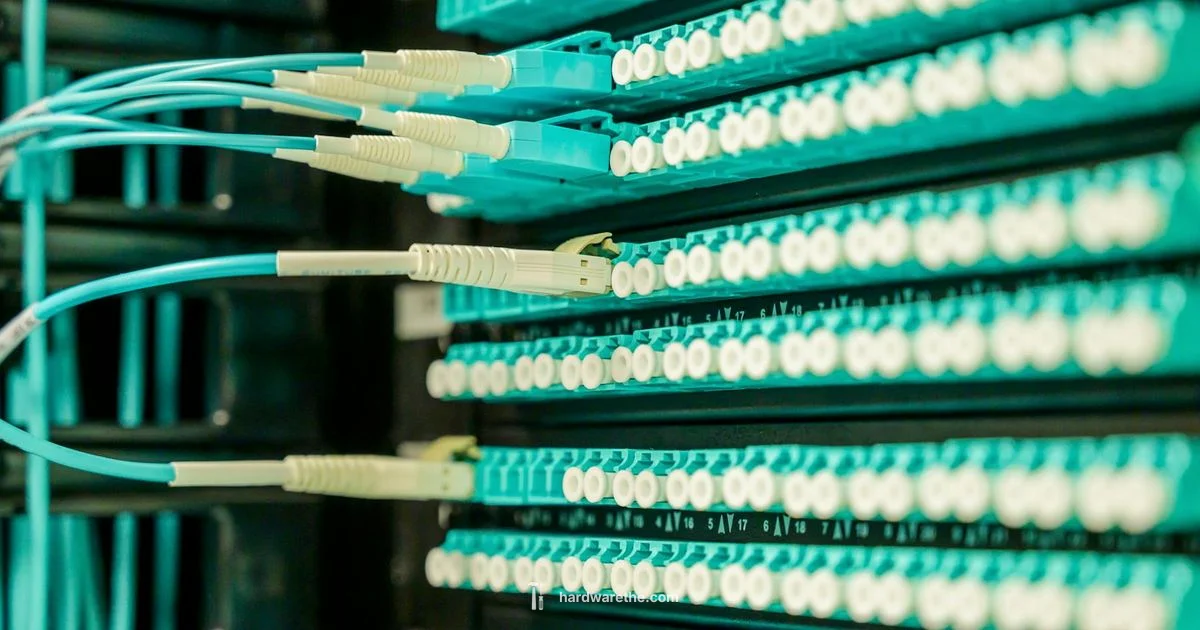
Firewall devices are built around a few core hardware blocks that determine how efficiently they can inspect traffic and enforce policies. The central processing unit (CPU) or system on a chip (SoC) handles rule evaluation, encryption, and logging. Sufficient memory is needed to maintain state tables for active connections, while storage supports logs and firmware images. Network interface cards (NICs) provide the ports for your network segments; many devices support multiple gigabit or multi gigabit ports with link aggregation. A robust power supply and reliable cooling extend the life of the hardware, especially in busy environments. Form factor matters too; compact units fit home offices, while rack-mountable appliances suit data centers or mid-market deployments. Redundancy features such as dual power supplies and hot-swappable fans improve uptime. Finally, consider management interfaces and secure access modes, because usable hardware is only as effective as its configuration tools.
Performance and scalability considerations
Performance and scalability hinge on more than raw speed. Real world throughput depends on policy complexity, number of concurrent sessions, and cryptographic tasks such as VPN and TLS offloading. Look for devices that report sustainable throughput under realistic rule sets and traffic patterns, not just peak numbers. Memory size and CPU architecture shape how many connections can be tracked without drops, while dedicated crypto engines or hardware acceleration can dramatically improve VPN performance. For growing networks, anticipate future needs and aim for headroom rather than chasing bottlenecks after deployment. Different environments emphasize distinct metrics: at home, VPN stability and parental controls matter most; small businesses need reliable threat prevention across multiple segments; larger networks require high availability, clustering, and centralized management. By aligning hardware capabilities with your anticipated workload, you get steady protection without needless overprovisioning.
Choosing between dedicated hardware vs generalized hardware
Dedicated firewall appliances are purpose-built for security tasks and often come with streamlined management, certified compliance features, and vendor support. They tend to be energy efficient and compact, with compact warranties and predictable performance. Generalized hardware can run firewall software on standard servers or mini PCs; this approach offers flexibility and potential cost savings, but it can complicate support, cooling, and reliability. In mixed environments, some organizations deploy a hybrid model: a dedicated gateway for perimeter protection plus secure software on a trusted server for additional functions. Whatever path you choose, verify compatibility with your network gear, ensure secure remote management, and plan for lifecycle costs, including firmware updates and spare parts. The key is balancing budget with required security features and long term scalability.
Home and small business deployment patterns
Home networks typically benefit from compact appliances with built in VPN and user friendly web interfaces. Small offices benefit from devices that combine firewalling with VPN, intrusion prevention, and simple central management. The Hardware analysis notes that misconfigurations are a common source of issues, so investing time in policy planning and regular audits pays bigger dividends than chasing the latest hardware model. In practice, set a clear topology: a single perimeter device at the network edge, with a separate internal segment if possible, and monitored logs to catch unusual activity. For wired and wireless setups, ensure that the firewall can enforce consistent policies across both domains and that access control lists reflect the actual security requirements of your space.
Network topology and placement
Where you place firewall hardware in your network affects both security and performance. The edge device typically sits between your ISP gateway or modem and your internal router, creating a bottleneck that governs all ingress and egress traffic. In larger networks, you might deploy a DMZ for publicly accessible services and a separate internal firewall for sensitive segments. Redundancy planning matters, with dual devices or clustering enabling failover. Plan cabling, power distribution, and cooling to avoid heat and outages. Management access should be restricted, preferably through a dedicated management network or VPN, with strong authentication and regular configuration backups. In all cases, document the network diagram and keep an asset inventory up to date to simplify troubleshooting and future upgrades.
Configuration and management best practices
Effective firewall management combines clear policy design with disciplined change control. Start with a baseline rule set that blocks all by default and only allows necessary traffic, then gradually broaden as required. Use descriptive rule names, document rationale, and implement versioned backups of policies. Enable logging and alerting for unusual activity, but avoid log overload by filtering what you store and monitor. Regular firmware updates and security patches are essential, as are tests of VPN tunnels, NAT rules, and failover procedures. Access should be tightly controlled: use role based credentials, multi factor authentication, and encrypted management connections. Maintain a written incident response plan and rehearse it with the team. Finally, schedule periodic audits to verify that the hardware remains fit for purpose and that security controls align with evolving threats.
Practical deployment example: a small home network
Step by step, here is a simple home network deployment. Step one, map the network: identify where the modem, router, and devices connect. Step two, choose a compact firewall appliance with VPN and basic threat prevention. Step three, place the device at the network edge, connect the WAN port to the ISP gateway and the LAN ports to your internal network switch. Step four, implement a minimal policy set that blocks unsolicited traffic and allows essential services; step five, enable secure remote management and create backups of the configuration. Step six, test the setup by simulating common tasks such as remote access, file sharing, and streaming. Step seven, monitor for alerts and adjust rules as needed. This approach yields a resilient baseline without overwhelming complexity, and you can scale up as needs grow.
Maintenance and lifecycle
Maintenance keeps firewall hardware effective over time. Schedule regular firmware updates, monitor health indicators and performance metrics, and verify that licensing and support agreements remain active. Have a lifecycle plan that anticipates hardware refresh and potential migration to a more capable device as traffic grows. Keep a documented change log and perform routine backups of both configuration and logs. For security, rotate credentials and review access controls periodically. Finally, include redundancy testing in your routine so you can confirm failover works as intended. The The Hardware team recommends treating firewall hardware as an evolving component of your security posture, with growth planning, regular audits, and proactive maintenance to stay ahead of threats.
FAQ
What is hardware for firewall?
Hardware for firewall refers to physical devices that enforce firewall policies and inspect traffic. It is distinct from software only solutions, offering dedicated performance and reliability.
Hardware for firewall refers to the physical devices that enforce firewall policies and inspect traffic, not just software running on a generic computer.
What is the difference between hardware firewall and software firewall?
A hardware firewall is a dedicated device designed specifically for security tasks, while a software firewall runs on general hardware. Hardware firewalls typically offer higher reliability and simpler management, whereas software firewalls can be more flexible but require careful maintenance.
A hardware firewall is a dedicated device, and a software firewall runs on standard hardware with flexible options.
Do I need redundancy for home setups?
Redundancy improves uptime but is often optional for home networks. If you host critical services or want maximum resilience, consider a second device or a backup configuration plan.
Redundancy helps uptime, but for most homes a single device is fine unless you host important services.
Can I reuse an existing router to act as a firewall?
You can enable firewall functionality on a router or run firewall software on a repurposed device, but dedicated firewall hardware often delivers better performance and security features.
You can use a router with firewall software, but dedicated firewall hardware usually performs better.
What performance metrics should I look at?
Look at sustainable throughput, VPN performance, and the number of concurrent sessions the device can handle. Real world tests and reviews help, too.
Check real world throughput, VPN speed, and how many connections the device supports.
Is cloud based firewall an alternative to hardware?
Cloud based firewall services are an option for some setups, but many networks still rely on edge hardware for control, latency, and privacy. A hybrid approach is also possible.
Cloud firewalls are another option, but edge hardware remains common for control and low latency.
Main Points
- Define your network needs before selecting hardware.
- Prioritize a balance of performance, reliability, and manageability.
- Different environments require different features such as VPN, IDS/IPS, and clustering.
- Plan for growth with scalable hardware and clear deployment topology.
- Maintain disciplined configuration management and regular firmware updates.