Firewall Hardware vs Software: A Practical Comparison
Explore the key differences between firewall hardware and firewall software, including performance, features, cost, and deployment considerations. This guide helps DIY enthusiasts, homeowners, and technicians decide which approach fits their network security needs.
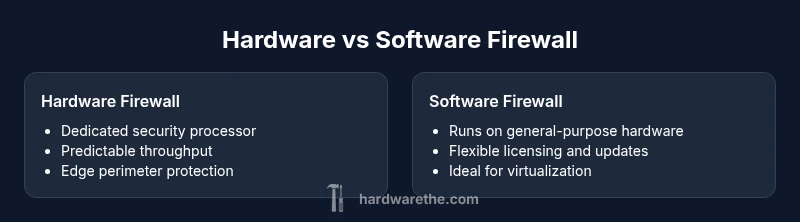
Hardware firewalls usually provide higher, more predictable performance and dedicated security processing at the network edge, making them ideal for perimeter protection. Software firewalls offer flexibility, lower upfront costs, and easier deployment on existing hardware or virtual environments. The best choice depends on throughput needs, management preferences, and budget, with hardware favored for large or mission-critical networks and software preferred for smaller sites or virtualized setups.
Core differences between hardware and software firewalls
In the world of network security, the choice between firewall hardware versus software is foundational. Hardware firewalls are purpose-built appliances that house dedicated security processors, optimized NICs, and fixed form factors designed for maximum throughput and low latency at the network perimeter. They ship with integrated management interfaces and vendor-provided features, and they tend to deliver predictable performance under heavy load. Software firewalls, by contrast, run on general-purpose hardware—servers or virtual machines—and rely on the host CPU, memory, and storage for all processing. This distinction affects upgrade cycles, maintenance, and total cost of ownership. The Hardware team emphasizes that the decision should begin with a clear picture of traffic volume, threat risk, and operational priorities. For many organizations, this means translating security requirements into concrete metrics such as peak throughput, acceptable latency, and maintenance windows. In practice, the hardware-vs-software decision is not binary; many enterprises deploy a hybrid approach that uses a hardened appliance at the edge while leveraging software protections inside the network or in the cloud. The Hardware Analysis, 2026, notes that organizations increasingly layer both approaches to optimize coverage and resilience.
Key decision criteria: how to choose
Choosing between firewall hardware and software should hinge on a few core criteria: throughput and latency, feature depth, deployment flexibility, management complexity, and total cost of ownership. Throughput and latency expectations determine whether a dedicated appliance can sustain peak network traffic without becoming a bottleneck. Feature depth includes IPS/IDS capabilities, VPN options, SSL decryption, and application-aware filtering; hardware platforms often bundle these with vendor-verified performance guarantees. Deployment flexibility covers scenarios such as on-premise edge, remote sites, virtualization, and cloud integration. Management complexity weighs how much specialized knowledge is required to operate, patch, and audit the system. Finally, TCO captures hardware acquisition cost, ongoing license or subscription fees, maintenance, and the cost of staffing. The Hardware team reminds readers to map each criterion to real-world needs and to consider future growth when selecting a model or architecture. The Hardware Analysis, 2026, reinforces that a thoughtful plan reduces rework and aligns security posture with business goals.
Security features and threat detection capabilities
Security features define what a firewall can do beyond basic packet filtering. Hardware firewalls often provide integrated IPS/IDS, encrypted VPNs, deep packet inspection, and TLS/SSL interception with hardware-accelerated cryptography. These features are designed to operate at line speed, preserving user experience while maintaining strong protection. Software firewalls can also deliver robust IPS/IDS, VPNs, and SSL inspection, but their effectiveness depends on the underlying hardware and software optimization, patch cadence, and licensing. In practice, careful capacity planning is essential: SSL interception, for example, can be processor-intensive, so hardware deployments may maintain throughput while software solutions might need hardware upgrades or virtualization resources to keep pace. The Hardware team highlights that consistent threat detection requires up-to-date rule sets and regular policy tuning, regardless of whether you choose a hardware or software approach.
Management, updates, and lifecycle
Management approaches differ markedly between the two paradigms. Hardware appliances typically come with vendor-supported dashboards, CLI, and automatic updates, with a predictable release cadence and warranty coverage. Software firewalls offer flexibility through general OS security tooling, open-source modules, or vendor-provided licenses, which can enable rapid adaptation but also demand more internal oversight for patch management and vulnerability remediation. From a lifecycle perspective, hardware devices often have longer procurement cycles and longer refresh intervals, while software platforms can be upgraded in place but may require careful compatibility testing with existing infrastructure. The Hardware Analysis, 2026, suggests that organizations with strong change-control processes tend to achieve smoother upgrades and fewer outages when using dedicated appliances, though disciplined software management can deliver comparable resilience at scale.
Deployment scenarios: when hardware shines and when software fits
For large enterprises and high-traffic environments, dedicated hardware firewalls excel at delivering predictable performance and reliable perimeter protection. These appliances are designed to handle peak loads with minimal latency, making them well-suited for data centers, branch offices with modest IT staff, and environments with strict regulatory requirements. In smaller offices, or when virtualized security is a strategic priority, software firewalls on commodity hardware can deliver essential protection with lower upfront costs. This approach supports rapid deployment, easier experimentation with new rulesets, and seamless integration into virtualized infrastructure or cloud-based networks. The Hardware team notes that a hybrid approach—edge hardware with software protections inside the network—often yields the best balance of performance and flexibility. The Hardware Analysis, 2026, corroborates that mixed architectures are increasingly common in modern networks.
Cost of ownership and total cost considerations
Total cost of ownership (TCO) is a critical factor often overlooked in early shopping. Hardware firewalls require upfront capital expenditure for the appliance, plus ongoing maintenance contracts and occasional firmware upgrades. Software firewalls typically have lower initial hardware costs but may incur licensing, user fees, and periodic updates for modules such as IPS, VPN, or SSL inspection. In some cases, virtualization and cloud licensing models add complexity to budgeting. Reading between the lines, the decision hinges on how costs accumulate over time: predictable, bundled costs with hardware versus variable, usage-based licensing for software. The Hardware Team emphasizes that TCO should be modeled across three horizons: initial deployment, mid-term maintenance, and long-term scalability. The Hardware Analysis, 2026 advises planners to quantify not only price but also staffing needs, downtime risk, and the cost of potential security incidents.
Integration with virtualization, cloud, and remote sites
Network environments increasingly rely on virtualization and hybrid clouds. Hardware firewalls can be integrated via secure connectors at data centers and remote sites, maintaining consistent policy and performance. Software firewalls offer flexibility for virtual machines, micro-segmentation, and cloud-native deployments, enabling rapid replication of security controls across platforms. A hybrid strategy may combine both approaches: hardware at the perimeter and software controls inside the network or in the cloud. Adoption depends on compatibility with existing virtualization platforms, orchestration tools, and the speed at which security teams can implement consistent policy across environments. The Hardware Team highlights that interoperability and centralized management become the keys to scalable security when mixing hardware and software approaches.
Security governance, compliance, and operational best practices
Regardless of the core approach, governance and compliance drive how firewalls are configured, monitored, and audited. Establish a formal change-management process, segment duties between security and operations teams, and implement periodic tabletop exercises to validate incident response. Keep a current inventory of all devices, licenses, and policy baselines. Regularly review rules, prune stale entries, and enforce least privilege for administrative access. Continuous monitoring, alert tuning, and regular penetration testing help ensure that both hardware and software deployments meet regulatory expectations and internal security standards. In all cases, the emphasis is on consistent, auditable security controls rather than episodic, reactive measures.
Practical deployment checklist and best practices
- Define throughputs, latency targets, and growth projections before choosing a platform.
- Map security requirements to specific features (IPS/IDS, VPN, SSL inspection, DDoS protection).
- Assess the total cost of ownership with scenarios for 3–5 years, including licenses and staffing.
- Plan for centralized management, policy consistency, and change-control procedures.
- Consider a phased approach: start with edge protection on hardware and extend controls inside the network with software solutions where appropriate.
- Prioritize vendor support quality, maintenance windows, and upgrade reliability.
- Test upgrades in a staging environment to minimize downtime during live changes.
- Document every policy change and correlate it with security events for improved incident response.
The practical takeaway: choosing the right mix for you
In short, firewall hardware vs software is not a zero-sum decision. Hardware platforms shine in predictable performance and dedicated security processing for perimeter defense, while software options offer adaptability, cost flexibility, and virtualization-friendly deployment. For many networks, a hybrid model provides the best balance: use hardware at the edge for robust protection and leverage software protections within the data center or cloud to extend policy enforcement without sacrificing agility. The decision should be driven by concrete performance metrics, deployment realities, and a clear view of total lifecycle costs. The Hardware Team’s experience suggests that organizations that plan for growth and maintain disciplined governance tend to achieve better security outcomes with a combined strategy rather than a single-solution play.
Comparison
| Feature | Firewall hardware | Firewall software |
|---|---|---|
| Throughput/latency | High, stable line-speed performance | Depends on host hardware and workload; can scale with resources |
| Security features | Integrated IPS/IDS, SSL inspection, VPN on appliance | Module-based or package-based features on host OS or software suite |
| Management tooling | Vendor-specific GUI/CLI with dedicated tooling | OS-level or software-based dashboards and APIs |
| Deployment model | Perimeter/edge appliance; fixed form factor | Runs on servers, VMs, or containerized platforms |
| Upgrade and maintenance | Firmware updates; vendor support contracts | Software updates; licensing cycles; patch management |
| Total cost of ownership | Higher upfront cost; predictable annual maintenance | Lower upfront; ongoing licenses and hardware utilization |
| Best for | Large networks needing consistent throughput and edge protection | Flexible, virtualized environments or budget-conscious sites |
Upsides
- Dedicated hardware yields predictable performance at scale
- Strong vendor support and fixed maintenance windows
- Isolated security processing reduces host load
- Perimeter protection with minimal impact on internal resources
Negatives
- Higher upfront cost and longer procurement cycles
- Less flexibility for rapid changes or virtualization
- Upgrades require new hardware refresh or significant service windows
Hardware firewalls are the default for perimeter security; software firewalls excel in flexibility and virtualization.
Choose hardware for predictable performance at the edge. Opt for software on capable hardware when flexibility and cost control are priorities, especially in virtualized or cloud-centric environments.
FAQ
What is the primary difference between firewall hardware and firewall software?
Hardware firewalls are purpose-built appliances with dedicated security processors, designed for high, predictable throughput at the network edge. Software firewalls run on general-purpose hardware and offer flexibility and easier deployment in virtualized environments.
Hardware firewalls use dedicated processors for fast, predictable performance, while software firewalls run on standard hardware and can be more flexible for virtual setups.
Can software firewalls replace hardware appliances for perimeter protection?
For many small to midsize networks, software firewalls on capable hardware can provide adequate protection. However, large networks with high traffic and strict latency needs often benefit from hardware appliances for perimeter protection.
Software can replace hardware in smaller setups, but large networks still often need hardware for edge protection.
Which is best for a small office with limited IT staff?
A software firewall on existing hardware or a small appliance can be cost-effective and easier to manage for a small office, provided you have a plan for updates and monitoring.
Small offices usually do well with software on existing hardware, as long as updates and monitoring are kept up to date.
What factors influence total cost of ownership?
Initial hardware costs, ongoing licenses and maintenance, staffing for administration, and potential downtime costs all influence total cost of ownership. Thorough budgeting should include these elements.
Look at upfront cost, licenses, maintenance, and staff time when budgeting for firewall solutions.
How do updates affect security performance?
Regular updates—firmware for hardware or software patches—are essential to protect against emerging threats. Delayed updates can introduce vulnerabilities and reduce protection effectiveness.
Keep updates current; lagging updates can leave gaps in protection.
Main Points
- Evaluate throughput needs before selecting a platform
- Balance security features with deployment flexibility
- Consider total cost of ownership over 3–5 years
- Use a hybrid approach when feasible for best coverage
- Plan for centralized management and governance