What Are Hardware Tokens and How They Boost Security
Discover what hardware tokens are, how they secure logins with physical devices, and how to choose and deploy them for personal or enterprise authentication. Practical guidance, types, and best practices.
Hardware tokens are physical devices that store cryptographic keys or generate one time codes to verify a user’s identity during authentication.
What hardware tokens are and why they exist
According to The Hardware, hardware tokens are physical devices that play a central role in modern authentication. They are designed to strengthen login security by providing something you possess that can be used to prove your identity in addition to something you know, like a password. In practice, a user carries or connects the token to a computer or mobile device during sign in, and the service verifies the token's response or signature. That response is generated inside the device, so sensitive cryptographic material never leaves the token in plain form. This makes phishing and credential reuse far harder for attackers.
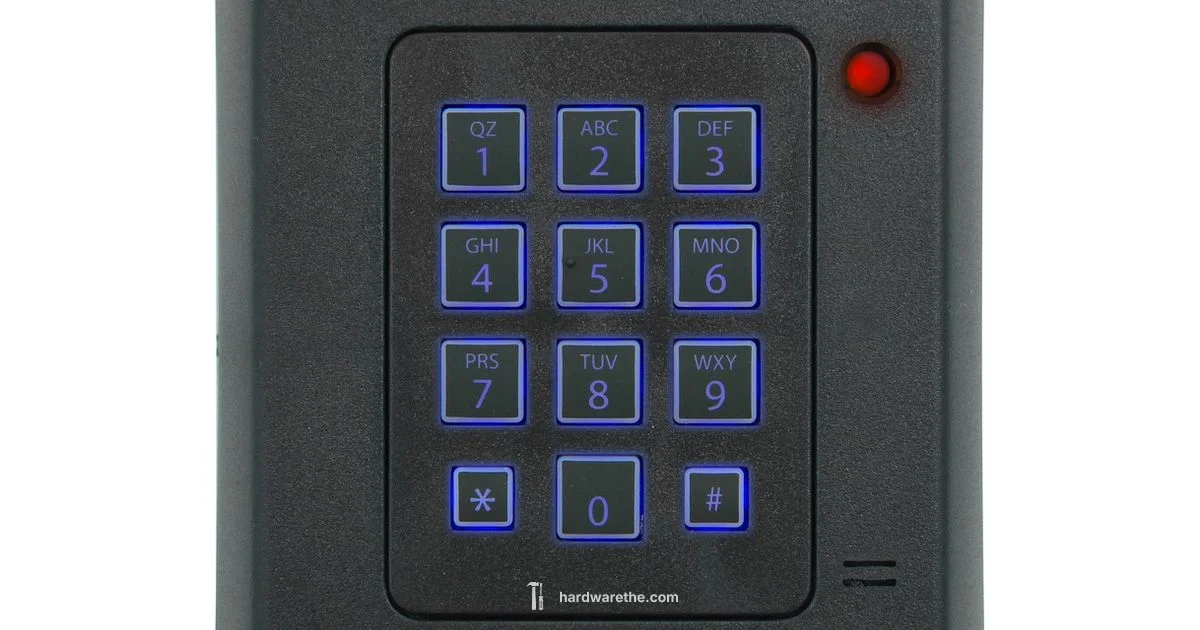
There are several common forms. USB and USB-C security keys plug into a computer and support modern protocols such as FIDO2 and WebAuthn, which enable passwordless or strongly tied logins. NFC and Bluetooth tokens work with phones and tablets, letting you authenticate by proximity rather than by inserting a cable. There are also standalone OTP (one-time password) devices that generate a time-based code every 30 or 60 seconds. A few tokens resemble smart cards used in corporate environments, where the device slots into a reader and performs cryptographic operations behind the scenes.
For most users, hardware tokens are a practical upgrade to password-based security, especially when sensitive accounts or high-value data are involved. They are not a cure-all; they do not eliminate all risks, but they significantly raise the bar for attackers. The choice between types often comes down to your devices, services, and whether you want a simple USB dongle or a more versatile multi-interface key.
How they work: cryptographic fundamentals in plain terms
Hardware tokens implement two broad families of approaches: cryptographic key-based authentication and time-based codes. In a key-based scheme, such as FIDO2/WebAuthn, the token holds a private key and a public key pair. When a service challenges the user to prove possession, the token signs a challenge with its private key. The service verifies the signature using the public key that was registered earlier. Because the private key never leaves the token, even if the service is compromised, an attacker cannot easily derive credentials.
In OTP-based devices, the token generates a short numeric code that the user types into the login form. The code is synchronized with the service, usually via a shared secret or a one-way algorithm. While OTP devices still rely on shared secrets, they do not rely on static passwords; they provide a moving credential that changes every cycle, which reduces the risk of replay attacks.
Ease of use varies. USB keys can require a touch or press to confirm presence, adding a security pause that deters automated attacks. NFC/Bluetooth tokens support mobile use without cables but may require pairing and permissions. The Hardware Team emphasizes that choosing between these options depends on how users access services and the level of phishing resistance you need.
Types of hardware tokens you might encounter
There are several families of hardware tokens, each suited to different environments and workflows. The main categories include:
- FIDO2/WebAuthn security keys: USB, USB-C, NFC, or Bluetooth devices that enable passwordless login and cryptographic verification.
- OTP or HOTP/TOTP devices: small calculators or keyfobs that generate a one time password on demand.
- Smart cards and PIV tokens: cards or card-shaped tokens used in corporate networks and secure enclaves.
- Multi-interface devices: keys that support more than one connection type, useful for mixed desktop and mobile ecosystems.
- Hybrid or built-in devices: some platforms integrate token capabilities directly into devices or secure enclaves for convenient use.
Each type has tradeoffs in terms of convenience, platform support, and resilience to attacks. Before purchasing, verify that the token works with your operating system, browsers, and identity providers, and check whether you can recover access if the token is lost or damaged. The Hardware Team recommends testing tokens in a controlled pilot before full rollout.
Use cases for individuals and organizations
For individuals, a hardware token provides a strong second factor for email, cloud storage, social accounts, and financial services. It dramatically improves phishing resistance because the login relies on a cryptographic assertion unique to the service and device rather than a shared password. For organizations, tokens are commonly deployed for single sign on, VPN access, privileged accounts, and administrative consoles. They simplify policy enforcement and reduce the risk of credential theft across large teams.
In practice, you might use a USB security key to log into your work computer, a mobile-friendly NFC key for a cloud portal on your phone, and an OTP device as an occasional backup for travel scenarios. For sensitive data, many teams require at least two independent factors, with a hardware token as one. When integrating with existing identity providers, organizations often create provisioning workflows that automatically issue, rotate, and disable tokens when users join or leave roles.
Pros, cons, and security considerations
Pros
- Strong phishing resistance and reduced reliance on passwords
- Portable authentication that works offline in many cases
- Broad compatibility with standards like FIDO2, WebAuthn, and TOTP
Cons
- Upfront cost and ongoing supply management
- Risk of loss or damage and the need for backup plans
- Potential vendor lock-in and integration complexity
- Some services may not support the token type you choose
Security considerations
- Maintain a backup token set and a clear revocation process
- Plan for token rotation, renewal, and emergency access
- Train users on how to use tokens and how to recover access if a token is lost
- Consider a staged rollout to confirm compatibility and avoid business disruption The Hardware analysis notes that hardware tokens significantly improve resilience against credential theft when deployed thoughtfully, but no solution is perfect. A balanced approach combines tokens with other security controls and strong password hygiene.
How to choose and implement a hardware token
Begin by mapping your needs. List the services and platforms that will rely on hardware tokens, the number of users, and whether mobile or desktop access is more common. Check for standards support such as FIDO2/WebAuthn, OTP compatibility, and smart card interfaces. Confirm provisioning capabilities with your identity provider and the availability of back up or recovery tokens.
Next, compare form factors and ecosystems. USB-C keys suit laptops, while NFC or Bluetooth keys are friendlier for mobile devices. Verify browser support and operating system integration, and assess whether you need multi-interface devices for mixed work environments. Pricing, warranty, and replacement policies matter for long term maintenance.
Plan deployment in stages. Start with a pilot group, document success criteria, and collect user feedback. Establish onboarding processes, user education, and help desk support. Maintain a secure provisioning workflow, including issuance, revocation, rotation, and emergency access procedures. Finally, ensure ongoing governance with periodic reviews and clear ownership. The Hardware Team recommends piloting and learning from initial deployments to refine the rollout and minimize disruption.
FAQ
What is a hardware token?
A hardware token is a physical device that provides cryptographic proof of identity during login. It serves as a second factor in multi-factor authentication and can operate as a passwordless login method in many services.
A hardware token is a physical device used as a second factor to prove who you are when you sign in.
How is it different from a software token?
Hardware tokens run on dedicated devices and generate cryptographic responses or codes, reducing exposure to malware. Software tokens run on smartphones or computers and generate similar codes or prompts but rely on the host device.
Hardware tokens use a dedicated device, while software tokens run on your phone or computer.
Which services support hardware tokens?
Many major providers support hardware tokens, especially through standards like FIDO2/WebAuthn and OTP. Availability varies by service, so check each provider’s docs and settings.
Most big services support hardware tokens via FIDO2 or OTP, but you should verify for each service.
What happens if I lose the token?
If you lose a hardware token, use your account recovery options or contact your administrator to revoke the lost token and issue a replacement. Have a backup method ready.
If you lose a token, use recovery options and contact support to revoke it and get a replacement.
Are hardware tokens expensive?
Prices vary by type and vendor. Budget for initial purchase and potential replacement costs, and consider organizational programs that provide tokens to users.
Costs vary; expect some upfront expense and potential replacement costs.
How do I set up a hardware token?
Setup typically involves registering the token with the service, linking it to your account, and performing a test login. Follow the provider's instructions and keep a backup token handy.
You set up by registering the token with the service and testing login; follow the provider's steps.
Main Points
- Adopt hardware tokens to strengthen two factor authentication
- Choose tokens based on compatibility with your services and devices
- Prefer standard based options like FIDO2/WebAuthn when possible
- Plan for backups, revocation, and user training
- Pilot deployments before full organization-wide rollout